
Cyber attacks are war.
Just invisible.
Strategic cyber advisory for boards. Translated into a language you already speak: terrain, tactics and decisions.
From expert jargon to concrete choices.
The board lacks a language
for cyber.
Cyber is among the biggest risk areas a board is responsible for. The fourth domain, alongside sea, land and air.
Yet it's described in a language that makes it hard to make good decisions.
Not because it's unimportant. Because it hasn't been translated.
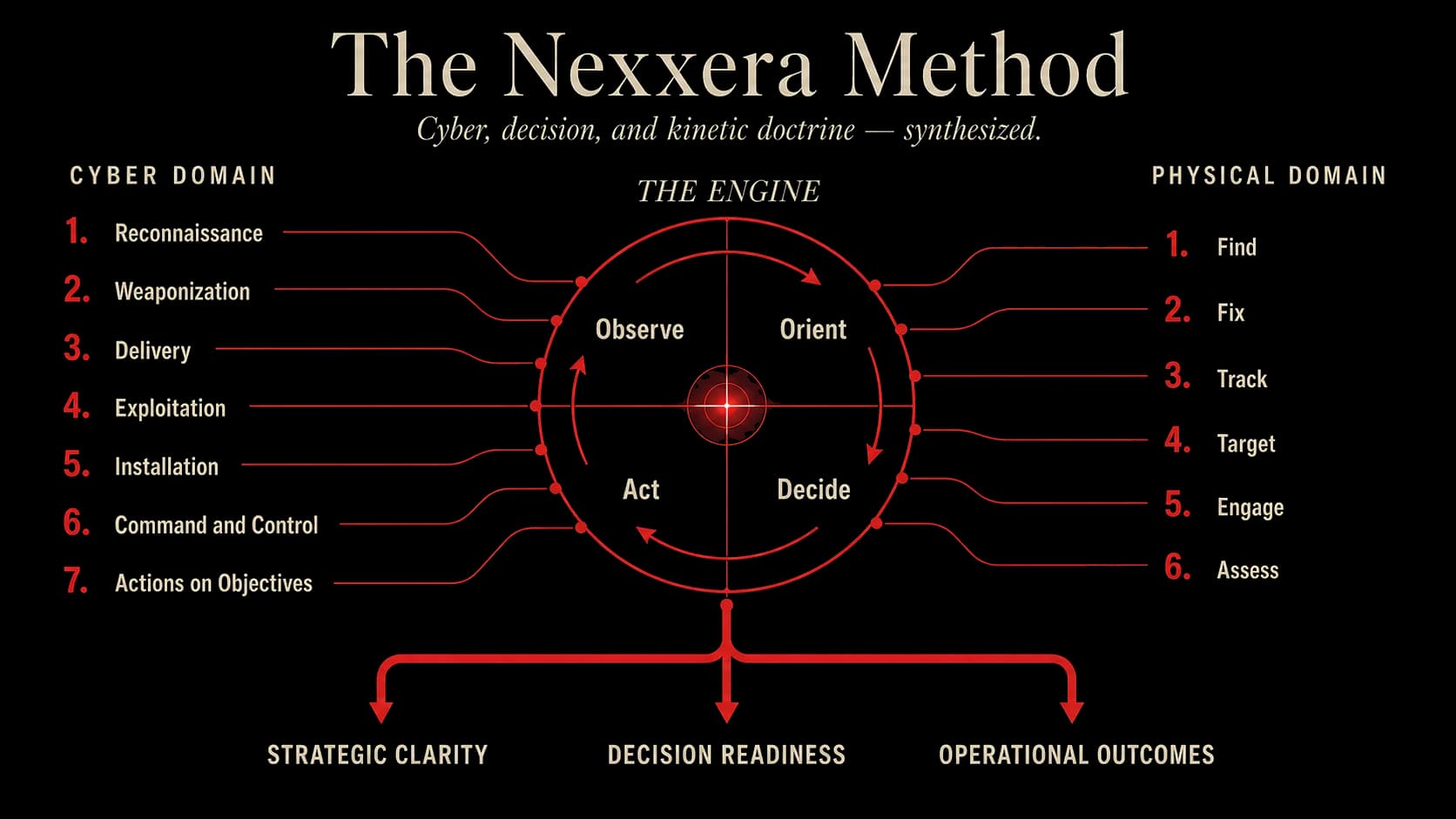
Built on the Cyber Kill Chain (Lockheed Martin), the OODA loop (John Boyd) and F2T2EA (Find, Fix, Track, Target, Engage, Assess).
We translate cyber into operational language.
The principles are the same. The domain is new.
We use maps, terrain and scenarios. That turns threats into something you can see, discuss and decide on. The terrain is made up of perimeter, networks, applications, hardware and databases, placed in zones according to how much control you have over them.
The same information. A different language.
Tracks the threat
Checklists are static and frozen in a single version. A terrain map updates the same day the threat picture shifts. You get a defence that follows reality.
Shared language
Boards read maps faster than reports. When everyone sees the same picture, the discussion shifts from terminology to priorities. Expert vocabulary stays with the experts.
Builds on NIST
We don't replace ISO 27001 or NIST. The map sits on top of them and translates what you're already obligated to do into something the board can actually decide on.
One workshop. One scenario.
You leave with a terrain map of your digital business, a threat simulation run on your map, a defence plan with scored measures and a decision document for the board minutes.
- 01
Orientation
We draw the business's digital terrain. What you have, where it sits, and who controls each part.
- 02
Assessment
We place the threat actors on the map. APTs, criminals, insiders and hacktivists have different motives and different routes in. We play through known attacks on your terrain.
- 03
Defence
We draw in the effects. What gets secured, what gets trained, what gets monitored, what gets controlled. Each effect is matched with concrete measures across technology, process or people.
- 04
Play
We test the plan against the threat. The board makes decisions in real time and scores the plan against five questions. The winning plan gets adopted.
Five questions your board should ask before approving a plan.
- Is it feasible?
- What can we accept?
- Do we see the whole picture?
- Have we thought smart enough?
- Is the plan suitable?
Each question opens up themes like ROI, residual risk, the RACI matrix, alternative approaches and future-proofing.
Book a strategic call.
30 minutes. No obligations. We talk about how you work with cyber today, and whether this adds value for you.